Why I built VSM-Cell.
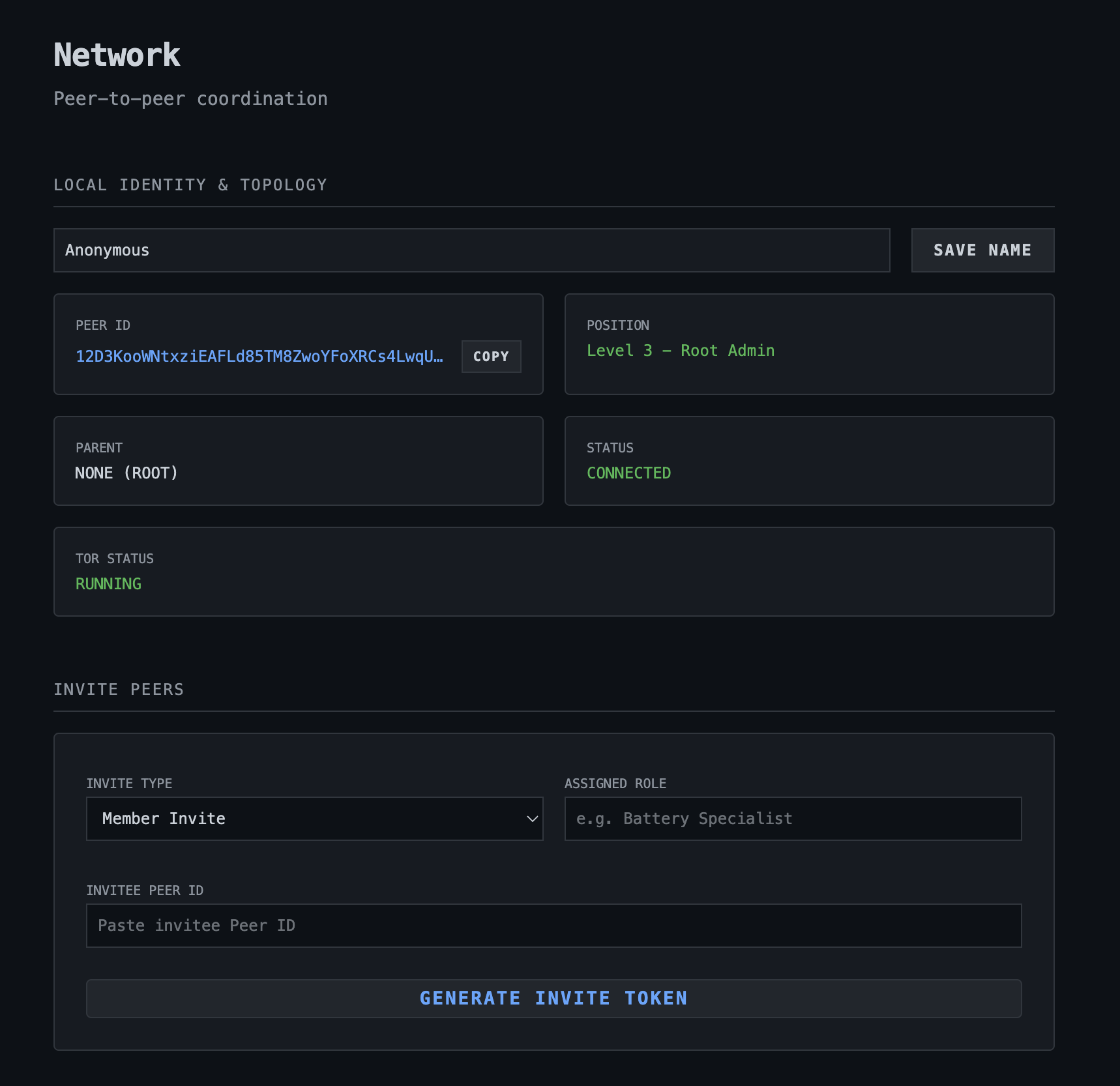
An exploration of VSM-Cell: A decentralized P2P mesh for AI agents using Tor-bundled Electron nodes, Noise Protocol handshakes, and Silent Drop security to build an invisible, autonomous network.
My concept was that of a business, where employees are available only from hour A to hour B, but where timezone mismatch might cause employee X to require information from employee Y, at an hour when Y is off work. In a globalized economy, timezone mismatches are inevitable. If Employee X in Tokyo requires critical project information from Employee Y in London, they are often forced to wait for an eight-hour overlap or interrupt Y’s personal time. I wanted to build a bridge across that gap that didn't rely on a centralized, vulnerable cloud database.
In this vision, Employee X doesn’t need to wake up Employee Y. Instead, X queries Y’s local VSM-Cell workspace. This node acts as a 24/7 digital twin or "agent-in-residence" that never sleeps. The agent can instantly retrieve available information from a designated "watch folder"—essentially the local project context—or execute complex tasks using an OpenClaw skill MCP (Model Context Protocol). Whether it's searching through local documentation, checking the status of a build, or summarizing a set of logs, the agent provides immediate, high-fidelity answers using the exact data Y left on their machine, all without the data ever leaving the private mesh.
To turn this from a complex networking experiment into a tool that anyone can actually use, I chose Electron as the foundation. However, the real "magic" happens under the hood with how I’ve handled the distribution. I’ve bundled the Tor daemon packages directly for both Windows and MacOS within the application's internal structure. This was a deliberate move to solve the "barrier to entry" problem that plagues most privacy-centric software. Usually, "anonymous P2P" involves a checklist of dependencies: "Install this, configure that, run this script." VSM-Cell throws that out the window.
The end-user experience is designed to be as frictionless as installing a standard chat app. You simply download the Windows .exe or MacOS .app, run it, and the system handles the rest. It automatically spins up a background Tor process, configures the hidden service, and generates your unique .onion identity in seconds. By shipping it as a pre-compiled, ready-to-use package, I’ve made it possible for a designer, a manager, or a developer to deploy a secure, anonymous AI node in any setting—from a home office to a locked-down corporate environment—without ever needing to touch a terminal or install Tor as a separate, visible entity on their system.
The Privacy Shield
Making a decentralized tool user-friendly is usually a bit of a challenge because running a P2P node typically forces you into a networking nightmare. You'd normally be stuck messing with manual port forwarding on your router, setting up Dynamic DNS, or using STUN/TURN servers that ultimately reveal your real-world IP address to a third party. For an agentic network designed to be "dark," this was unacceptable. By bundling the Tor daemon directly into the VSM-Cell executable, the entire infrastructure layer is effectively abstracted.
When you launch the app, it doesn't just start a UI; it initializes a local SOCKS5 proxy and spins up a hidden service, eliminating the "IT guy" requirement entirely. There are no firewall exceptions to write and no UPnP settings to toggle because the node tunnels out through the Tor network, establishing a bidirectional communication channel that works even behind the strictest corporate deep-packet inspection. In this architecture, your identity is your address; every node is identified by a .onion address derived from its public key, meaning your physical location and metadata are shielded by three layers of onion routing.
Traffic is bounced through three distinct nodes globally to ensure that no single point in the network knows both the source and the destination of the agent's data. Since the Tor network can be volatile, a custom "Heartbeat" mechanism is implemented, where the node performs a health check on its active circuits every 45 seconds. If it detects latency spikes or a dropped connection, it triggers a self-healing pulse that automatically re-establishes a new circuit and re-announces its presence to the mesh. This happens entirely in the background, ensuring your AI agents remain reachable even if the underlying network topology shifts.
Security through Silence: The "Ghost Node" Philosophy
In the world of cybersecurity, visibility is the first step toward a breach. Most traditional servers operate on a "Talk First, Authenticate Later" basis where they acknowledge a connection request and then ask for credentials, but even a rejection is a signal that tells an attacker something is there. VSM-Cell operates on a Silent Drop policy, leveraging the Noise Protocol Framework to move the security boundary to the very first packet of the handshake.
We use a specific handshake pattern (AES-GCM/ChaChaPoly) where the initiator must prove they possess a pre-shared or authorized key before the responder sends a single byte of data back. This ensures that the communication is not only encrypted from the jump but also mutually authenticated. Every cell is a private club; if an incoming handshake message isn't signed with a valid Ed25519 key that your specific node recognizes, the system doesn’t send back an "Unauthorized" error—it sends back absolutely nothing.
By silently dropping unauthenticated packets, the node becomes a "Ghost." To an external port scanner or a malicious actor trying to probe the network, your machine appears as if it isn't even connected to the internet. There is no service to exploit because, as far as the network stack is concerned, the service doesn't exist for unauthorized users. This security through silence makes the mesh incredibly resistant to mass-surveillance crawlers and targeted DDoS attacks, providing a sanctuary for agents to exchange sensitive project context in total peace.
VSM-Cell as a Programmable Building Block
For the developer, VSM-Cell isn't just a standalone application; it functions as a headless infrastructure layer that effectively abstracts away the most grueling parts of distributed systems. When you are architecting an agentic system, you are almost always sidelined by the "networking tax"—the endless friction of NAT traversal, managing static IPs, or wrestling with VPN configurations just to get two entities to talk. VSM-Cell operates as a sidecar for your AI agents, solving these connectivity and security hurdles silently in the background. By exposing an internal Model Context Protocol (MCP) interface, the system allows you to plug in OpenClaw orchestration directly, turning the cell into a "black box" for secure, anonymous communication. Because the stack is built on the Noise Protocol and pre-bundled Tor daemons, any application you build on top of it inherits total network invisibility without you having to write a single line of socket-level code.
This architecture enables a form of orchestration that requires zero traditional infrastructure. You can use OpenClaw to define complex, multi-agent tasks while VSM-Cell handles the heavy lifting of peer-to-peer discovery and encrypted transport across the mesh. This opens the door for seamless skill injection; a developer can extend a cell's capabilities simply by dropping new MCP skills into the local environment—be it a specialized database connector or a custom hardware interface. The agent residing within the cell can then utilize these tools while remaining completely shielded behind its .onion identity. Ultimately, this replaces the need for a traditional REST API. Instead of maintaining a public-facing URL and the massive overhead of OAuth, your project simply "dials" another VSM-Cell via its public key, effectively turning the entire internet into a flat, secure local network where your code can run in peace.
Next Steps: Moving Toward the Headless Mesh
While the Electron app makes VSM-Cell accessible for anyone with a laptop, the real power of a decentralized network lies in its persistence. If we want a mesh that truly never sleeps, we can't rely solely on desktop computers being left open. That’s why the immediate next step for the project is a CLI-only version designed for headless deployments.
By stripping away the Chromium overhead of Electron, I’m building a lightweight binary that can run on minimal hardware—think Raspberry Pis, home servers, or hidden VPS instances. This CLI version will act as a "Permanent Cell" in the firm’s hierarchy; a silent, low-power node that maintains the mesh's connectivity 24/7. It will handle the same Tor-bundled transport and "Silent Drop" security, but it's built to stay in the shadows of a server rack rather than on a taskbar.
The goal is to allow users to "seed" their private network. You could have a headless node in your office that constantly indexes your main documentation and another at home, creating a personal, invisible cloud that you can access from your laptop anywhere in the world. As I move toward this headless architecture, the focus remains on making the deployment as simple as the desktop version: a single command to spin up a sovereign, anonymous agentic node.
I’m currently refining the terminal interface and the remote management protocols for these headless cells. If you’re interested in P2P systems or want to help test the early CLI builds, the repo is open for business.